





80% Faster document processing
“Working with you guys has been amazing. We don't have to guess as much what customers are searching for because we have an AI piece to it as well.”
read the full story
Outcomes Compliance Ops Teams Can Count On
Your Compliance Department Stops Operating In Silos
Your Examiners Find No Gaps Between Functions
Your Officers Spend Their Day On Judgment, Not Assembly
BSA officers review instead of drafting from scratch, fraud investigators start with a structured file, and KYC analysts clear onboarding queues without backlog.
How Any Compliance Function Produces A Regulator-Ready File
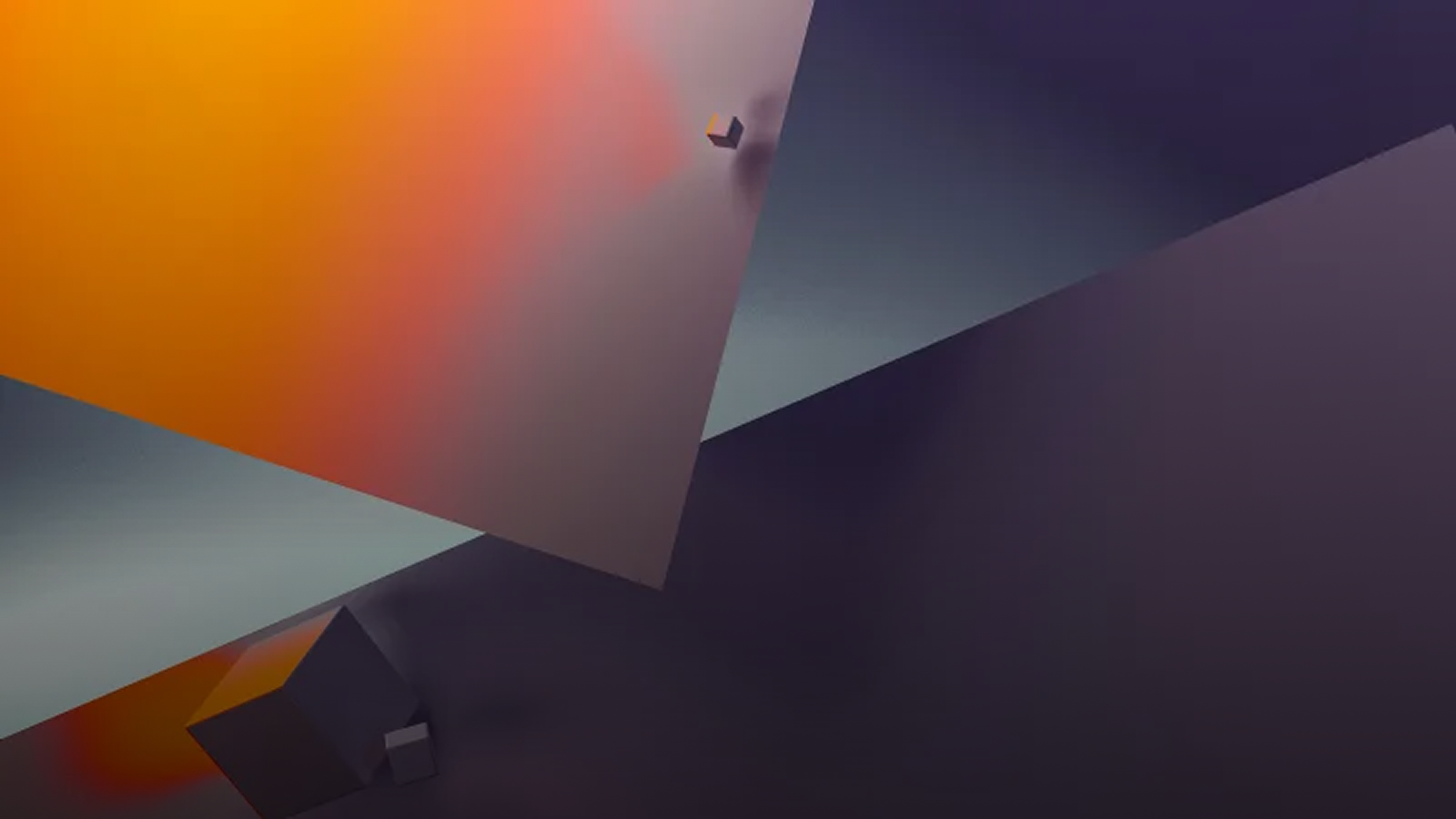
ACH/Wire Validation
Screen incoming and outgoing ACH and wire transfers against OFAC lists, internal watchlists, and transaction limits. Flag anomalies, validate beneficiary details, and generate audit-ready logs.
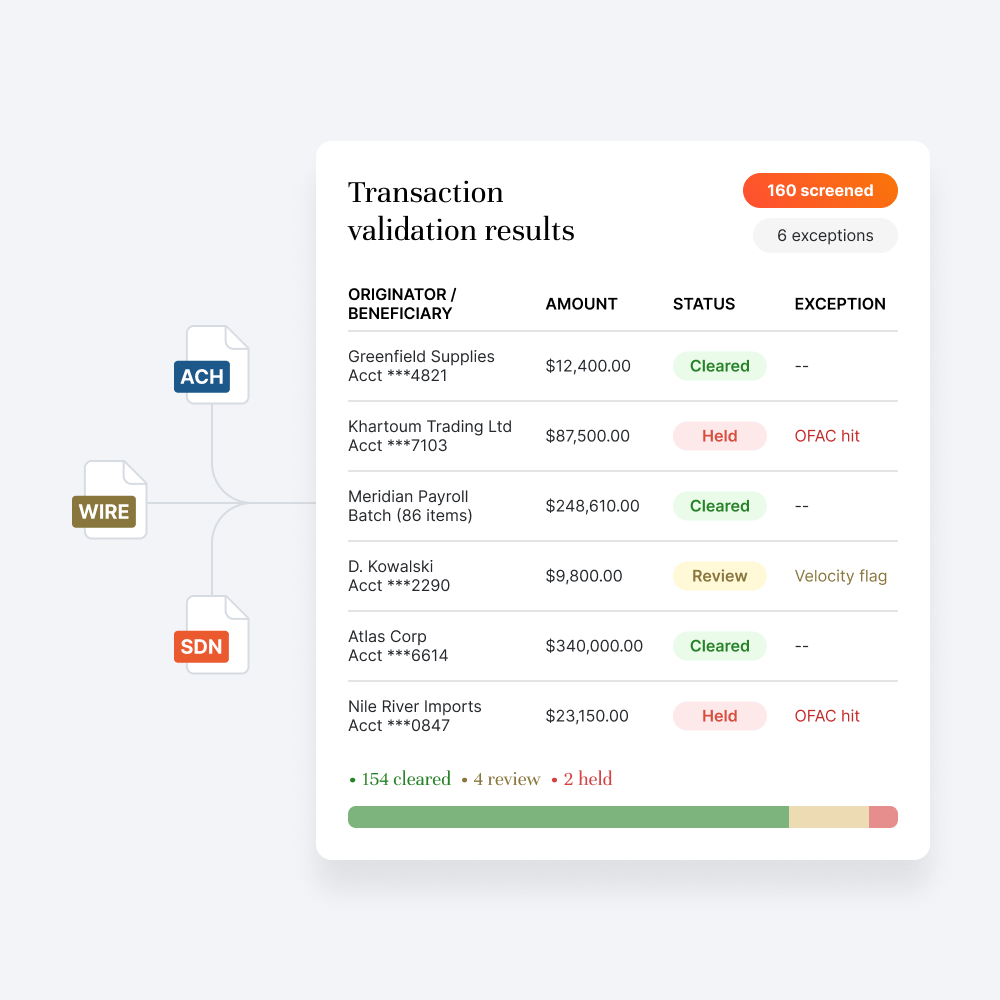
Business Account Opening
Extract entity data from formation documents, verify beneficial ownership, run KYB screening, and produce a complete account opening package with risk classification and compliance sign-off.
Fraud Investigation & Resolution
Consolidate transaction data, communications, and dispute records into a single investigation file. Build event timelines, cross-reference accounts, and generate findings reports for resolution.
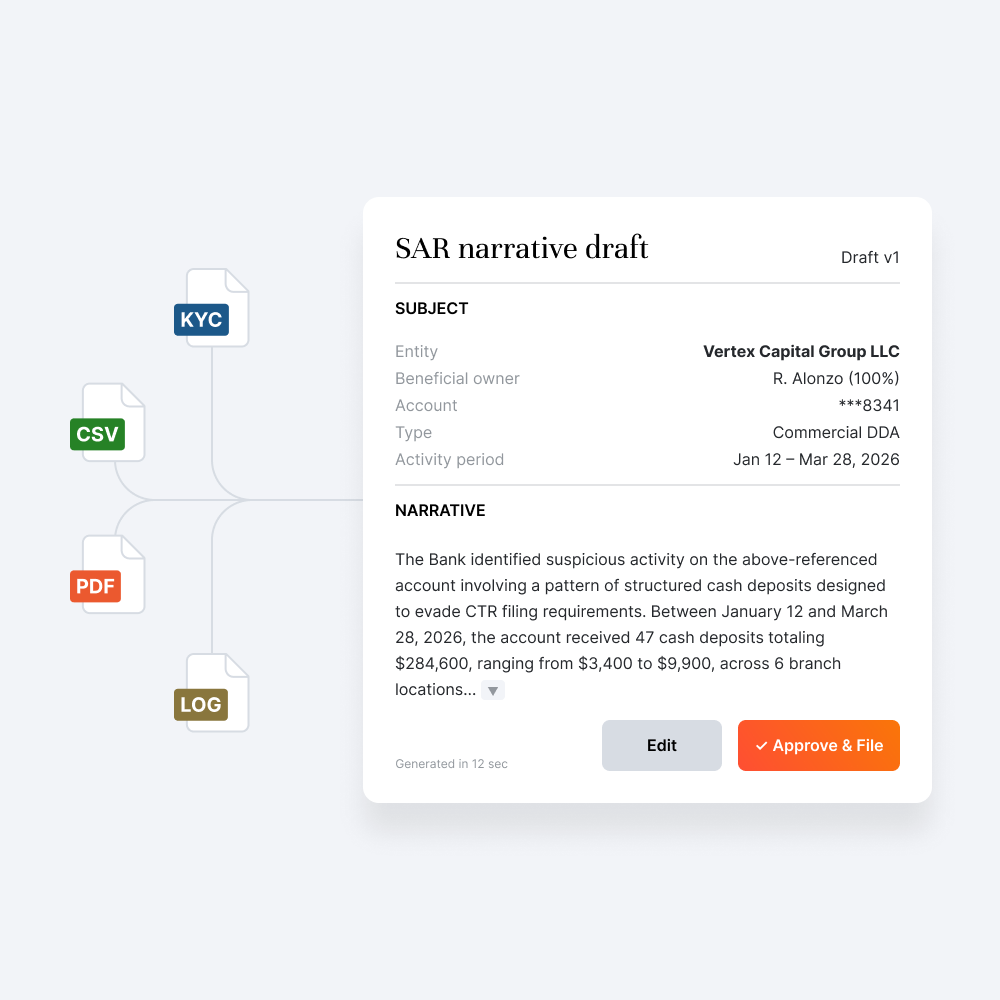
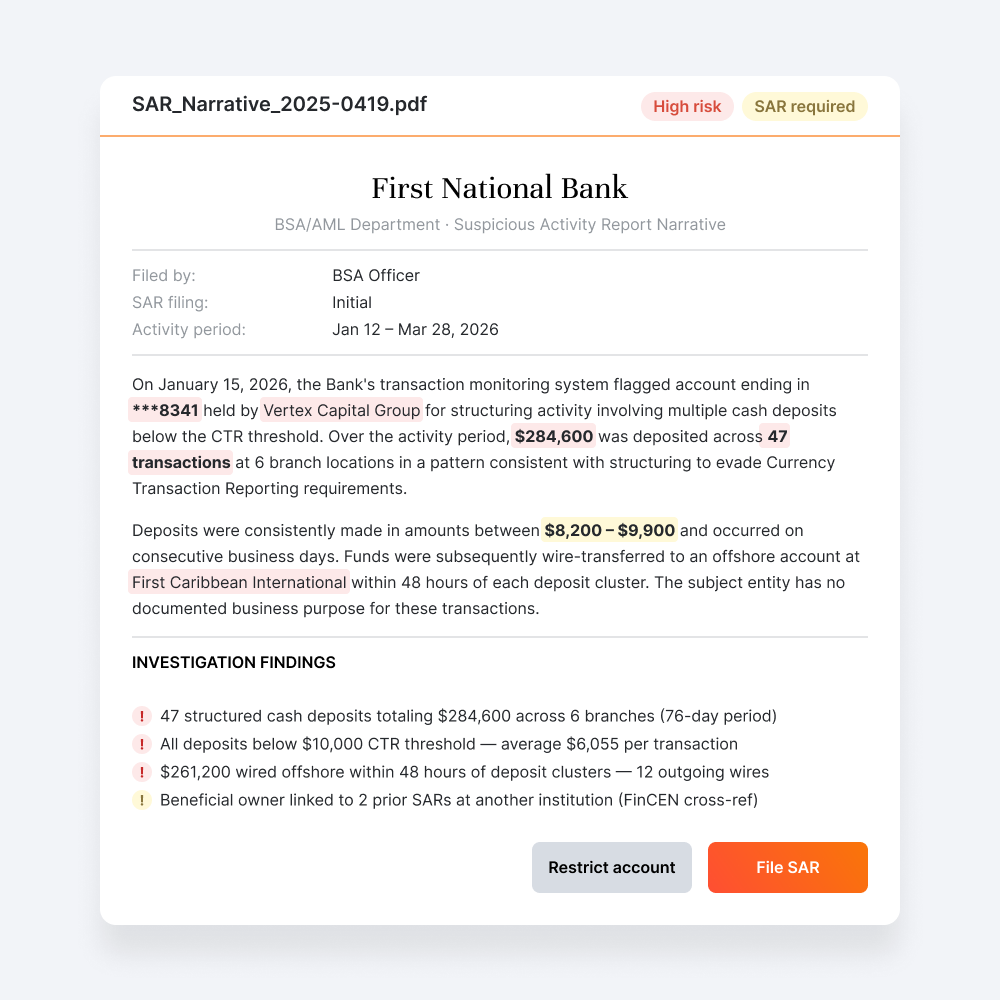
SAR Narrative Drafting
Borrower data extracted, TRID timelines confirmed, and HMDA fields validated, the mortgage lending automation your compliance team needs, built into every residential file
Every Compliance Discipline Your Department Relies On
BSA Officers
Compliance Analysts
Fraud Investigators
Payments and Deposit Operations
Vendor Risk Managers
Chief Compliance Officers
Plug Into Legacy Systems Without Rip-And-Replace








Evidence And Audit Trails On Every Case

SOC 2 Type II
Single-Tenant Deployment
Zero Data Retention
BSA/AM
FinCEN
Reg E
Reg CC
OCC
FDIC
NCUA
Turn One Messy Case Into A Review-Ready File, Live
FAQs
Yes. Pre-built compliance automation workflows cover 24 case types across BSA/AML, account onboarding, deposit operations, fraud and risk, payments, and third-party risk management.
Yes. KYC processes, risk tiers, SAR thresholds, CTR triggers, EDD criteria, and vendor risk classifications all configured to your compliance policies.
Continuous monitoring workflows track activity patterns, flag threshold breaches, and update risk assessments automatically, your compliance analysts review exceptions, not raw data.
Yes. Encryption in transit and at rest, role-based access, and zero data retention by default, customer PII and transaction data stay governed by your policies throughout.
Human review is built into every workflow. Analysts override any output, overrides logged with reason codes and preserved in the audit trail, keeping every file defensible.
Yes. Case outputs and risk flags flow into your existing stack, Jack Henry, Fiserv, FIS, and your compliance management systems, via secure integrations.
Yes. Available under NDA as part of your vendor management or procurement review.
Each playbook applies the requirements specific to that function, FinCEN anti-money laundering criteria for SAR filing, Reg E timelines for fraud resolution, Reg CC rules for deposit holds.
Yes. Every investigation runs inside your institution's governed environment, PII, transaction records, and case documentation stay under your control from intake to closeout, with zero data retention by default.

.svg)